Cyber Insurance – Complementary or proactive service (Part 3).
This is a breakdown of the four services that I’m considering Tier 1 worthy, here we go.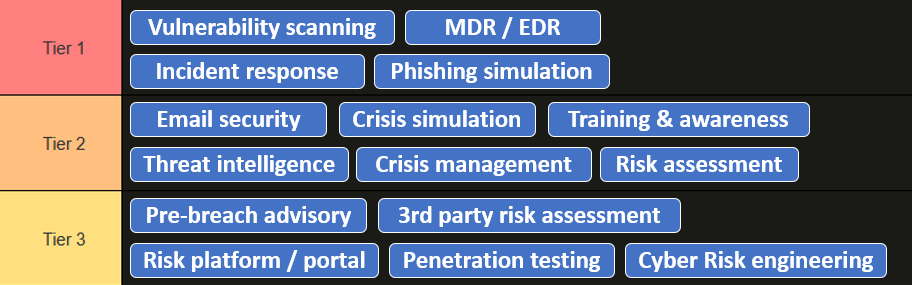
Tier 1
Phishing simulation - Phishing is the dominant delivery mechanism for credential theft and ransomware across all major claims datasets. Simulation with measured feedback loops demonstrably reduces click rates in a way that passive training does not — because it creates a consequence and a learning moment at the point of failure. It’ placed below Incident Response because the effect is probabilistic and degrades without repetition. A single annual simulation has limited durable impact; the Tier 1 reflects consistent, programme-level delivery.
Phishing can be highly realistic and tailored to activities within your individual company, it can leverage your professional or personal interests, it can rely on massive ongoing events like world cup, war, elections, epidemic or a (disappointing) finale of the Stranger Things to lure you into clicking.
The more exposure your employees will have in a controlled environment – more cautious they will be in real life.
Incident response - Pre-contracted 24/7 Incident Response directly reduces claims cost post-event. Every uncoordinated hour after a breach multiplies forensic costs, legal exposure, and regulatory liability. It scores slightly behind the two remaining services because it is reactive — it reduces severity after an incident starts rather than preventing one. A product that only offers Incident Response and nothing else is still providing meaningful value, but less than one that prevents incidents from occurring.
It’s hard to tell how sophisticated the particular on-call support is - it can be fully outsourcing to commercial SOCs, it can be in-house, it can be rather high level and scripted, it can be hands on.
But insurers acknowledge the massive impact on the cost of the incident, making 24/7 hotline by far the most represented complementary services across all insurers globally. Even insurers that don’t have anything else – often have it.
MDR/EDR - The second-highest in Tier1 because it addresses dwell time, which is the primary driver of ransomware severity. A threat detected in hours versus weeks is the difference between a contained incident and a catastrophic loss. It is the most expensive service to procure independently ($15K–$80K+/yr for SMEs) and is fully operational — threats are contained, not merely flagged. It scores slightly below the next one because it requires compatible endpoint tooling to already be deployed, which limits reach across the clients. Still a massive and reliable cyber blanket against the threats of the digital world.
Vulnerability scanning - The king of Tier 1 because it directly addresses the most common initial access vector across all claims datasets: unpatched systems, misconfigured and exposed services. It is operationally expensive to run continuously ($10K–$50K/yr for a managed service), and it produces a concrete, actionable list of specific vulnerabilities with remediation references. It still requires action on client side, but it’s continuous, it’s preventive in nature, it significantly reduce the attack surface for an attacker. Bonus points for addressing compliance requirements, that otherwise would be pricey to implement.